Security Team Inbox
profuseclabs@gmail.com
Every layer engineered against modern threats—so your mobile experience stays secure, resilient, and trusted.
We use modern Mobile frameworks and reactive architectures to build fast, secure, cloud-native applications.
Optimized for mobile performance and security compliance, delivering smooth UX and protection against modern threats.
We don't just claim to build secure mobile apps — we've delivered it again and again. From hardened architectures to active threat defense, our apps are already securing people worldwide.
Secure mobile application development with focus on data protection, encryption, and real-time threat monitoring for enhanced user privacy.
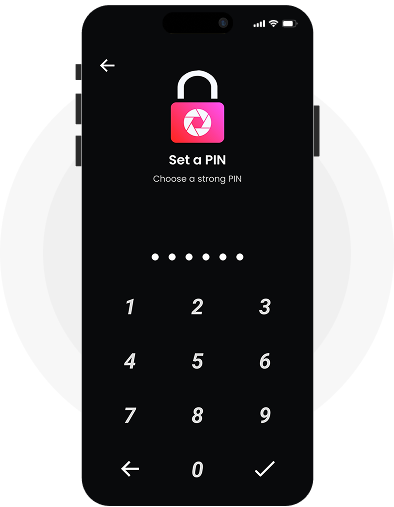
We leverage Trusted Execution Environments (TEE) and hardware-backed keys to isolate sensitive operations from the OS.
This ensures encryption and authentication remain tamper-proof and inaccessible to external threats.
Our systems follow NIST-recommended algorithms for encryption and hashing.
Every layer is validated for strength, compliance, and resistance to cryptographic attacks.
We integrate quantum-safe key exchanges to secure data against future computational threats.
This future-proofs confidentiality far beyond classical encryption methods.
Layered code obfuscation conceals logic and encryption routines from reverse engineering.
It prevents analysis, tampering, and unauthorized access to core functions.
Real-time monitoring detects hooking, debugging, and injection attempts instantly.
Apps can respond, defend, or safely terminate under threat.
Zero-trust architecture secures every app–server connection through encrypted channels.
Data stays protected in transit and at rest with verified authentication.
Enterprise-grade mobile security solutions featuring hardware-level protection, NIST-approved cryptography, quantum-resilient design, advanced obfuscation, runtime protection, and secure cloud integration for comprehensive threat defense.
Connect directly with security experts, threat researchers, and hardened developers building the future of mobile protection.
profuseclabs@gmail.com
Dedicated security consultation for large organizations
Comprehensive mobile application security assessment
Contact our mobile security defense team for secure application development, threat analysis, encryption consultation, and enterprise security solutions.